The shift to remote work has transformed how we approach business operations, bringing incredible flexibility and new opportunities for organizations worldwide. However, this transformation also introduces significant cybersecurity challenges that many companies struggle to address effectively. Remote workers often access company data from various locations, use personal devices, and connect through unsecured networks, creating potential vulnerabilities that cybercriminals actively target.
The good news is that with the right security measures in place, you can protect your remote workforce while maintaining the productivity and flexibility that makes remote work so valuable. Build a robust framework that protects your team, your clients, and your operations with these tips for keeping your remote workforce secure.
Implement Multi-Factor Authentication for All Accounts
Multi-factor authentication stands as your first and most critical line of defense against unauthorized access to company systems. This security measure requires users to provide multiple forms of verification before gaining access to accounts, making it exponentially more difficult for cybercriminals to breach your systems even if they obtain employee passwords.
This additional step prevents the vast majority of account takeover attempts and significantly reduces your organization’s risk exposure. The implementation process involves configuring MFA settings for all business applications, email accounts, and cloud services your team uses regularly.
Use a Virtual Private Network to Secure Internet Connections
A VPN creates a secure, encrypted tunnel between your remote employees and your company’s network infrastructure. This technology ensures that all data moving between remote workers and company systems remains protected from interception, even when employees connect through public Wi-Fi networks or unsecured home internet connections.
Remote workers frequently access the internet from various locations, including coffee shops, co-working spaces, and public areas where network security may be compromised. A VPN encrypts all internet traffic, making it virtually impossible for cybercriminals to intercept sensitive business communications or data transfers. Additionally, VPNs help mask your employees’ actual IP addresses and locations, adding another layer of privacy protection that helps prevent targeted attacks based on geographic information.
Provide Regular Cybersecurity Training for Employees
Your employees represent both your greatest security asset and your most significant potential vulnerability. Regular cybersecurity training transforms your workforce into an active defense mechanism that can identify and prevent security threats before they impact your organization. This training should cover current threat landscapes, common attack methods, and practical steps employees can take to protect themselves and company data.
Effective cybersecurity training goes beyond basic awareness and provides hands-on experience with real-world scenarios. Employees learn to recognize phishing emails, understand social engineering tactics, and know how to respond when they encounter suspicious activities. Regular training sessions ensure that your team stays current with evolving threats and maintains strong security habits. Consider conducting monthly training sessions and periodic simulated phishing tests to reinforce learning and identify areas where additional training may be needed.
Establish Clear Data Security Policies and Procedures
Clear, comprehensive data security policies provide your remote workforce with specific guidelines for handling sensitive information and maintaining security standards. These policies should address data classification, acceptable use of company resources, incident reporting procedures, and consequences for policy violations. Well-defined policies eliminate ambiguity and ensure that all team members understand their security responsibilities.
Your data security policies should specifically address remote work scenarios, including guidelines for working from public locations, using personal devices, and storing company data on local drives. Include procedures for reporting security incidents, steps for secure file sharing, and requirements for software updates and system maintenance. Regular policy reviews and updates ensure that your guidelines remain relevant as your remote work arrangements evolve and new security challenges emerge.
Conduct Routine Security Audits and Vulnerability Assessments
Regular security audits help you identify weaknesses in your remote work infrastructure before cybercriminals can exploit them. These comprehensive assessments examine your entire security posture, including network configurations, access controls, software vulnerabilities, and compliance with security policies. Routine audits provide valuable insights into the effectiveness of your current security measures and highlight areas that need improvement.
Vulnerability assessments focus specifically on identifying technical weaknesses in your systems and applications. These assessments use automated tools and manual testing techniques to discover potential security gaps that could allow unauthorized access to company data. Schedule these assessments quarterly or after significant changes to your remote work infrastructure. The results help you prioritize security improvements and allocate resources effectively to address the most critical vulnerabilities first.
Enforce Strong Password Policies and Regular Password Updates
Strong passwords form the foundation of effective cybersecurity, yet many organizations still struggle with weak password practices among remote workers. Comprehensive password policies should require complex passwords that include uppercase and lowercase letters, numbers, and special characters. Additionally, passwords should meet minimum length requirements and avoid common dictionary words or personal information.
Regular password updates help limit the potential damage from compromised credentials. Even if cybercriminals obtain employee passwords through data breaches or other means, regular password changes can prevent long-term unauthorized access to company systems. Consider implementing password managers to help employees create and maintain strong, unique passwords for all their accounts. These tools eliminate the burden of remembering multiple complex passwords while ensuring that each account has robust password protection.
Secure All Remote Access Points
Remote access points represent critical vulnerabilities that require constant attention and monitoring. Every connection point between remote workers and your company network must be properly secured and continuously monitored for unusual activity. This includes VPN connections, remote desktop services, and cloud application access points.
Monitor for Suspicious Activity
Implementing comprehensive monitoring systems helps you detect potential security breaches in real-time. These systems can identify unusual login patterns, multiple failed authentication attempts, and access from unexpected locations. Automated alerts notify your security team immediately when suspicious activities occur, enabling rapid response to potential threats. Regular monitoring also provides valuable data for improving your security policies and identifying trends that might indicate emerging threats.
Partner with a Managed Services Provider to Secure Communications
Managing cybersecurity for a remote workforce can overwhelm internal IT resources, especially for smaller organizations or those without dedicated security expertise. Managed services providers help support remote teams through enhanced cybersecurity, proactive monitoring, optimized resources, and more.
A qualified MSP can help implement and manage many of the security measures discussed in this guide, from endpoint protection to network monitoring. These partnerships provide scalable security solutions that grow with your remote workforce while ensuring that you always have access to current security technologies and expertise. MSPs also provide valuable support during security incidents, offering rapid response capabilities and specialized knowledge for complex security challenges.
Securing your remote workforce requires a comprehensive approach that addresses technical, procedural, and human factors. Start implementing these measures today to keep your remote workforce secure and protect your business from evolving cyber threats.










 Deering Estate
Deering Estate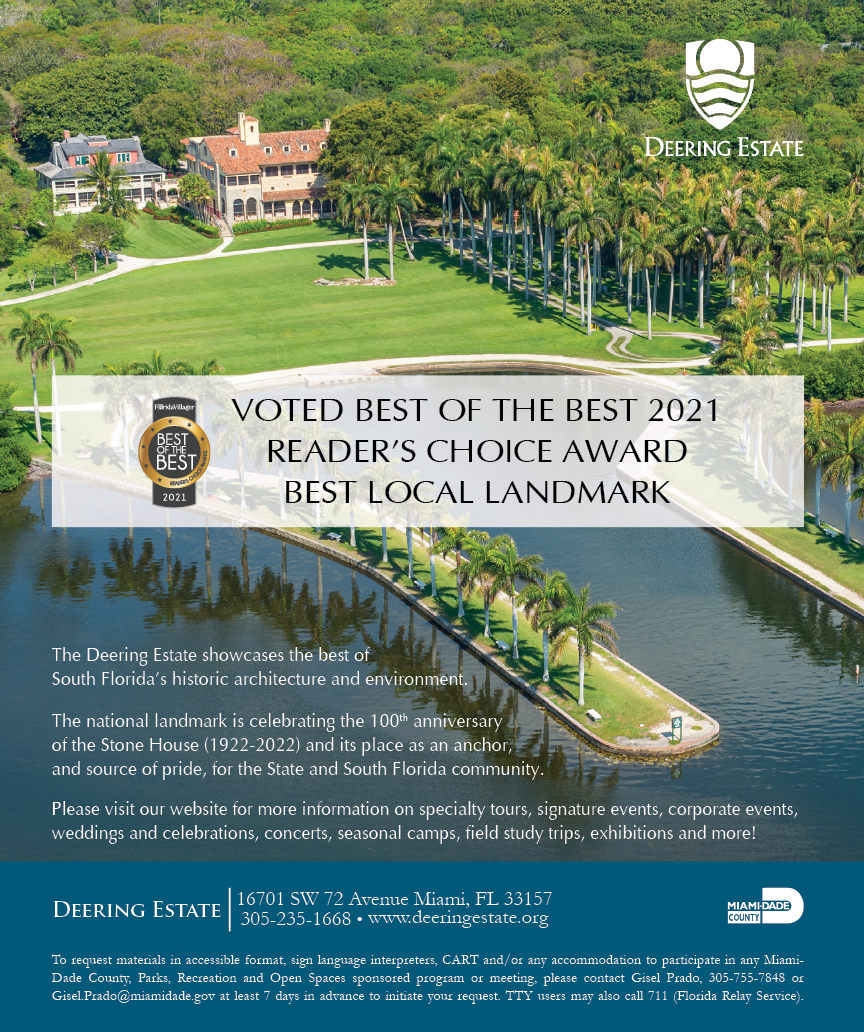
 Massage Envy South Miami
Massage Envy South Miami
 Calla Blow Dry
Calla Blow Dry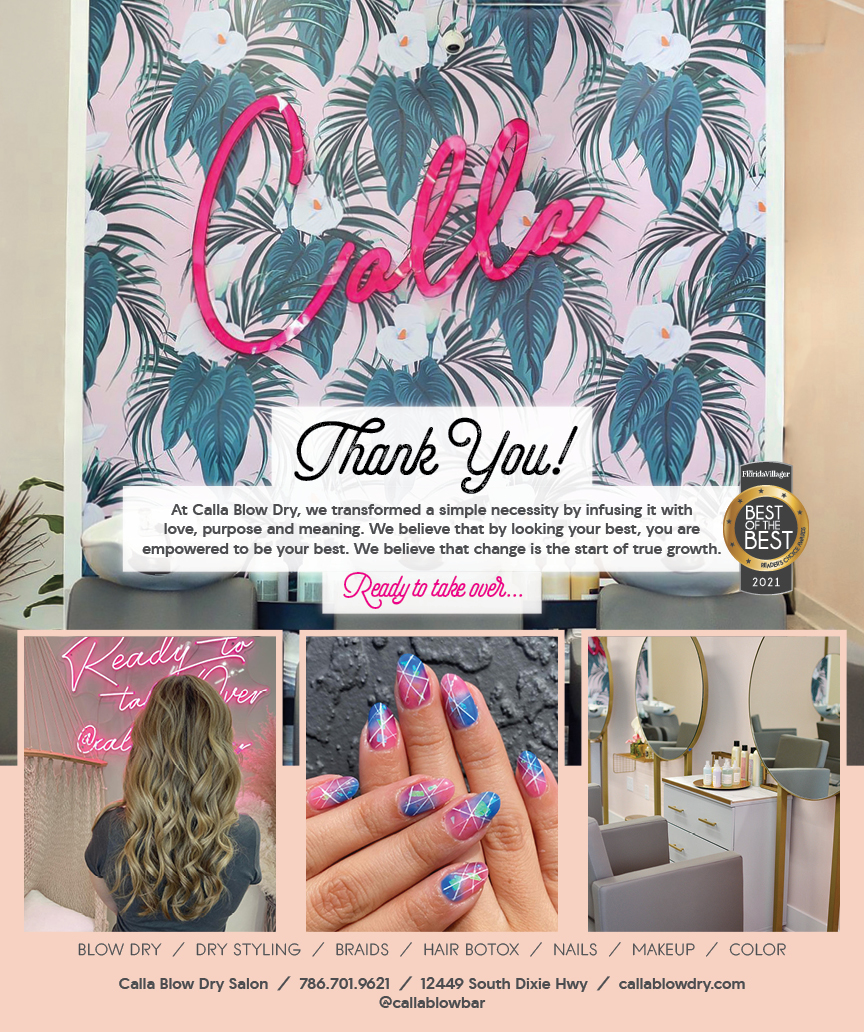
 My Derma Clinic
My Derma Clinic
 Sports Grill
Sports Grill
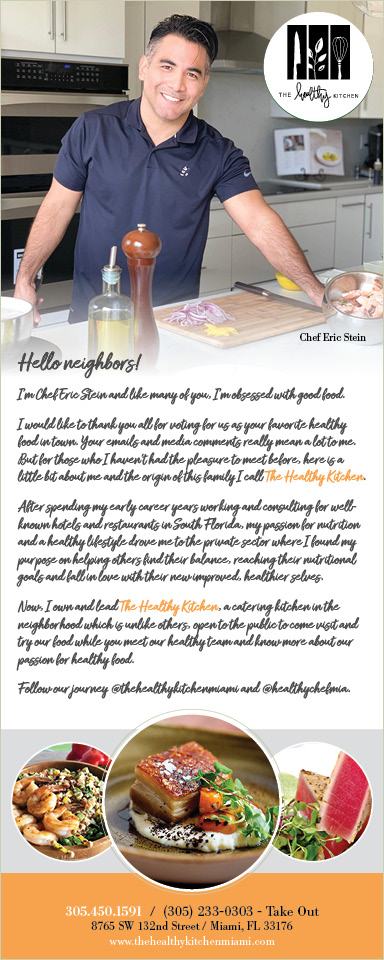
 The Healthy Kitchen
The Healthy Kitchen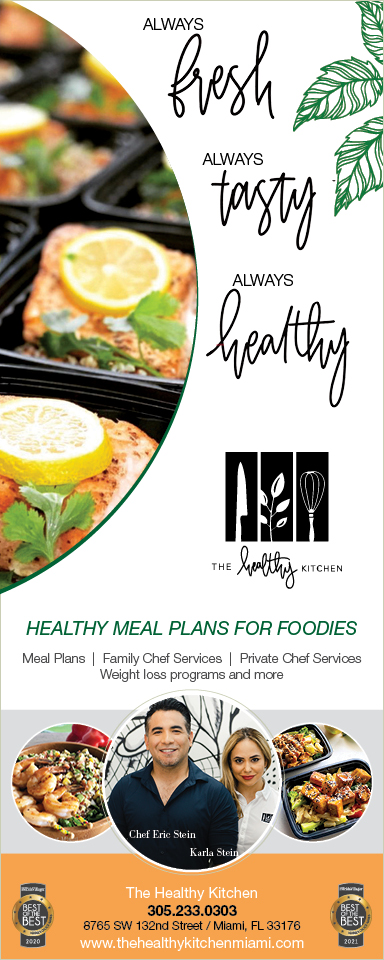
 Sushi Maki
Sushi Maki
 Golden Rule Seafood
Golden Rule Seafood
 Malanga Cuban Café
Malanga Cuban Café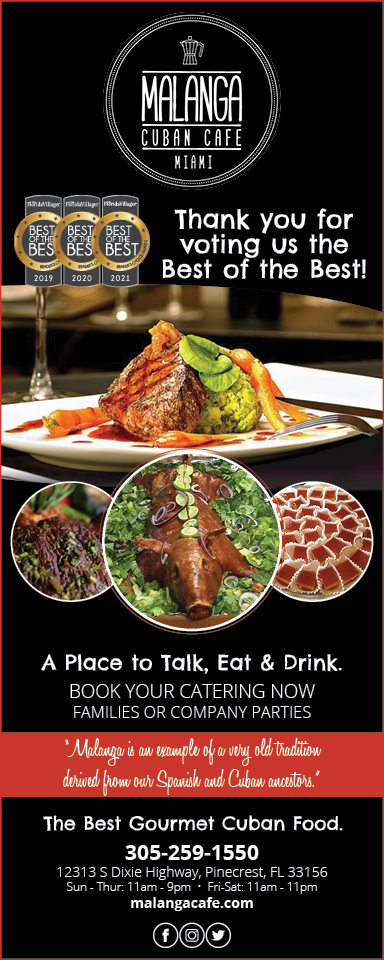

 Kathleen Ballard
Kathleen Ballard
 Panter, Panter & Sampedro
Panter, Panter & Sampedro
 Vintage Liquors
Vintage Liquors
 The Dog from Ipanema
The Dog from Ipanema
 Rubinstein Family Chiropractic
Rubinstein Family Chiropractic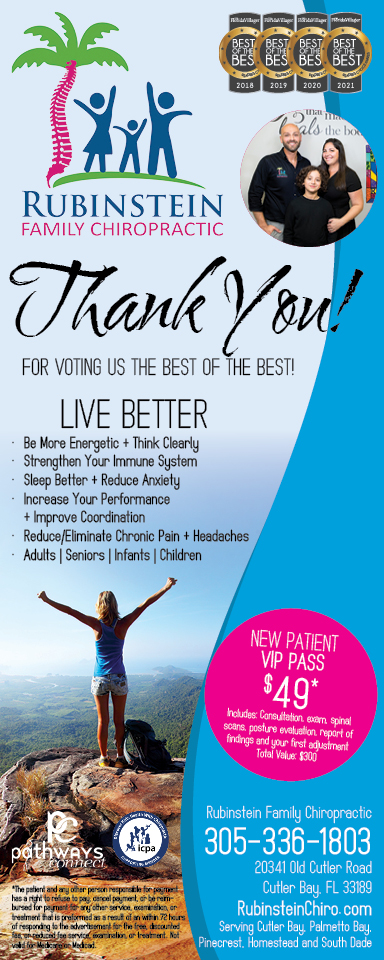
 Your Pet’s Best
Your Pet’s Best
 Indigo Republic
Indigo Republic


 ATR Luxury Homes
ATR Luxury Homes


 2112 Design Studio
2112 Design Studio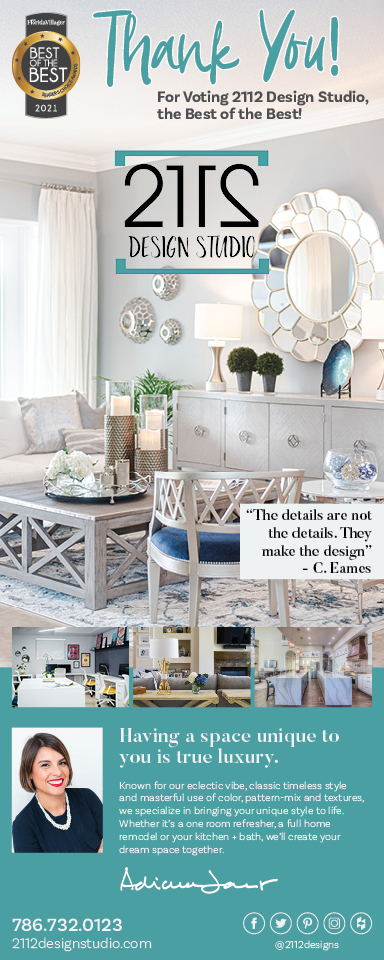
 Hamilton Fox & Company
Hamilton Fox & Company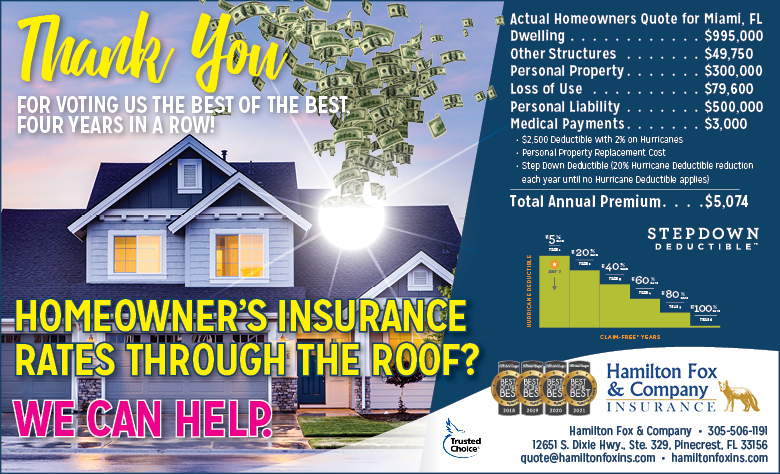
 Creative Design Services
Creative Design Services
 Best Pest Professionals
Best Pest Professionals
 HD Tree Services
HD Tree Services
 Trinity Air Conditioning Company
Trinity Air Conditioning Company
 Cisca Construction & Development
Cisca Construction & Development
 Mosquito Joe
Mosquito Joe
 Cutler Bay Solar Solutions
Cutler Bay Solar Solutions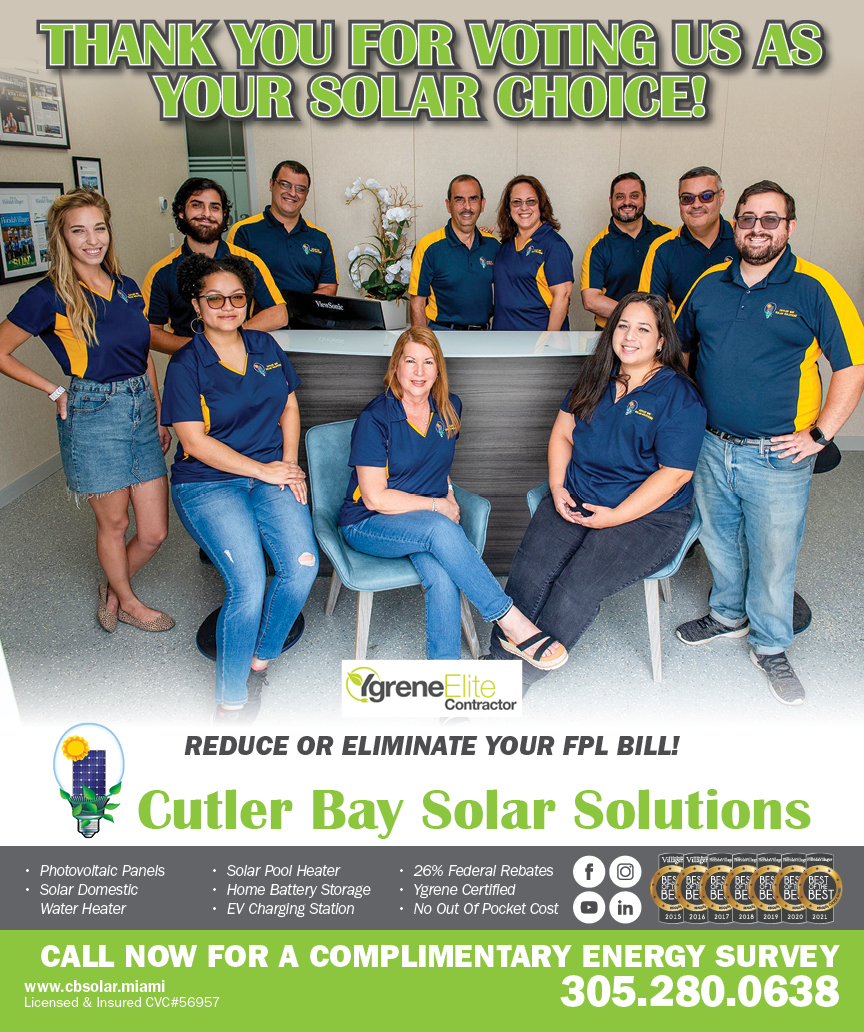


 Miami Royal Ballet & Dance
Miami Royal Ballet & Dance
 Christopher Columbus
Christopher Columbus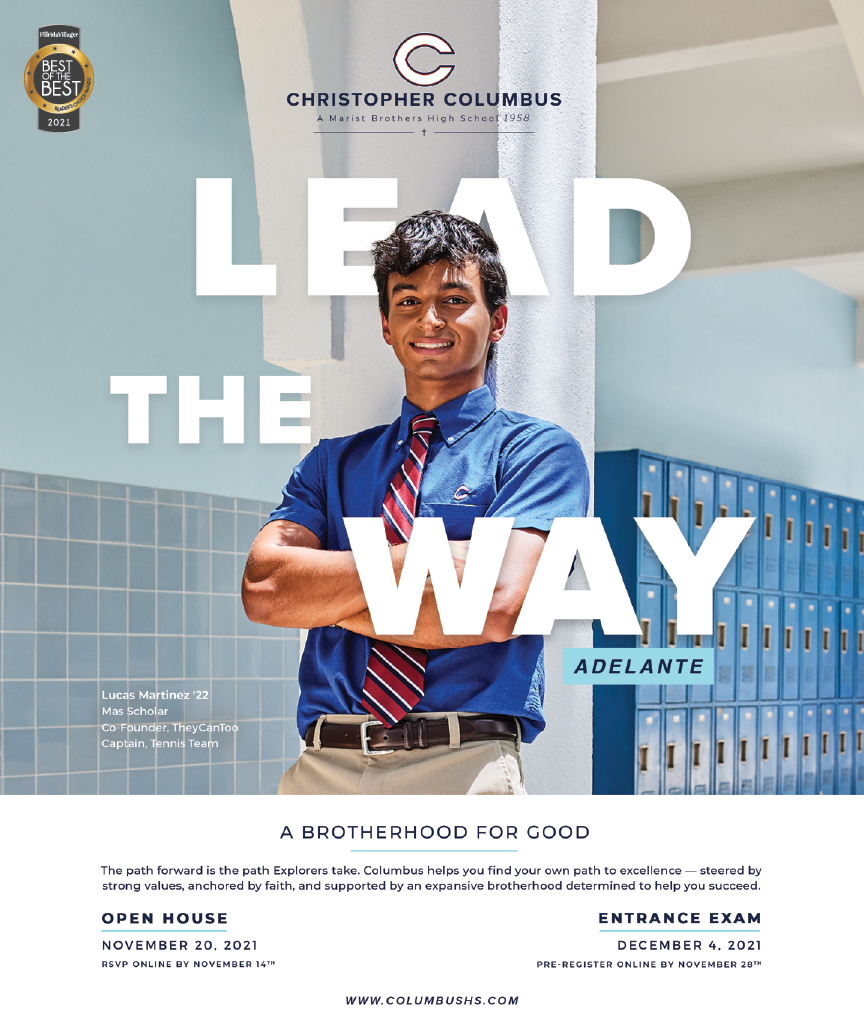
 Pineview Preschools
Pineview Preschools
 Westminster
Westminster
 Carrollton
Carrollton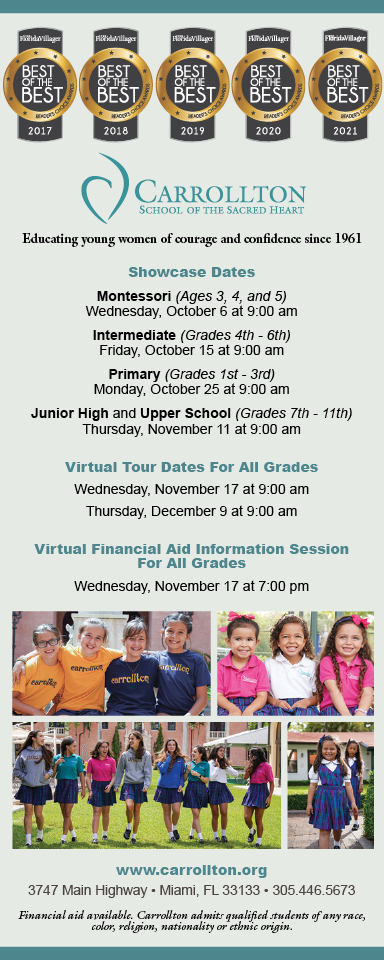
 Lil’ Jungle
Lil’ Jungle
 Frost Science Museum
Frost Science Museum
 Palmer Trinity School
Palmer Trinity School
 South Florida Music
South Florida Music
 Pinecrest Orthodontics
Pinecrest Orthodontics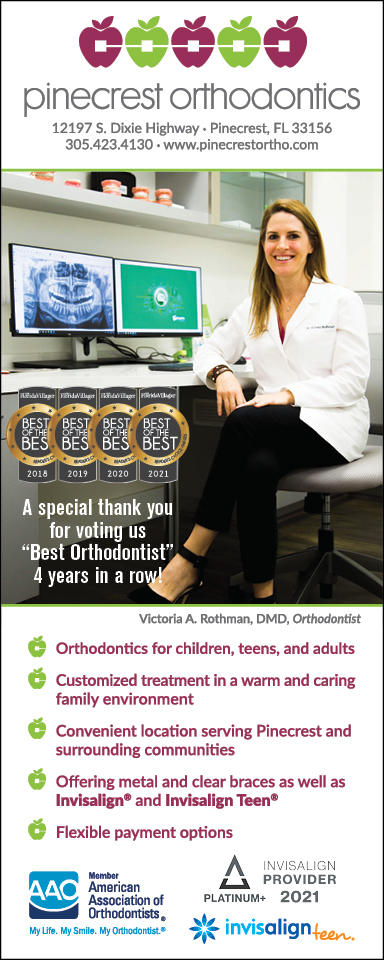
 Dr. Bob Pediatric Dentist
Dr. Bob Pediatric Dentist
 d.pediatrics
d.pediatrics

 South Miami Women’s Health
South Miami Women’s Health
 The Spot Barbershop
The Spot Barbershop
 My Derma Clinic
My Derma Clinic


 Miami Dance Project
Miami Dance Project

 Rubinstein Family Chiropractic
Rubinstein Family Chiropractic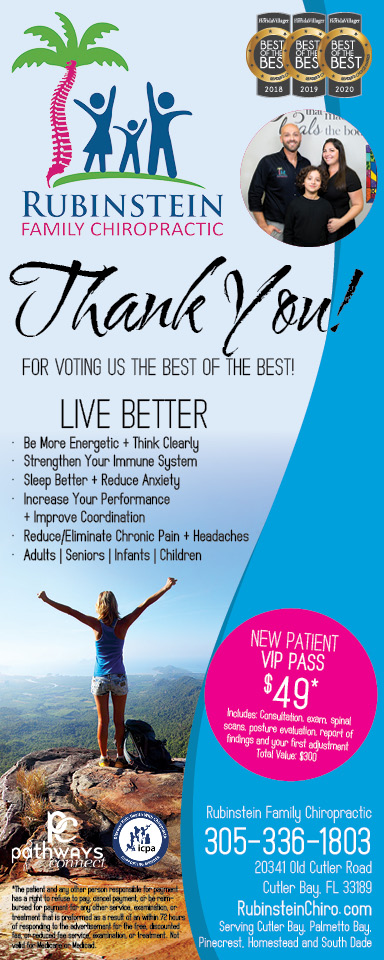
 Indigo Republic
Indigo Republic

 Safes Universe
Safes Universe
 Vintage Liquors
Vintage Liquors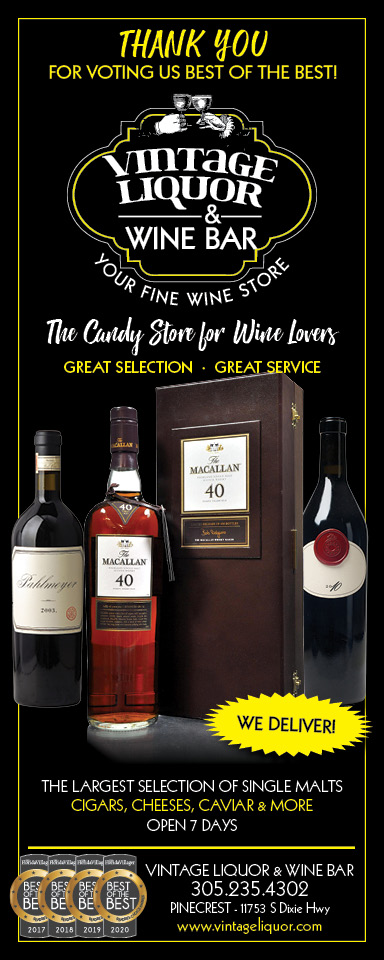
 Evenings Delight
Evenings Delight




 Atchana’s Homegrown Thai
Atchana’s Homegrown Thai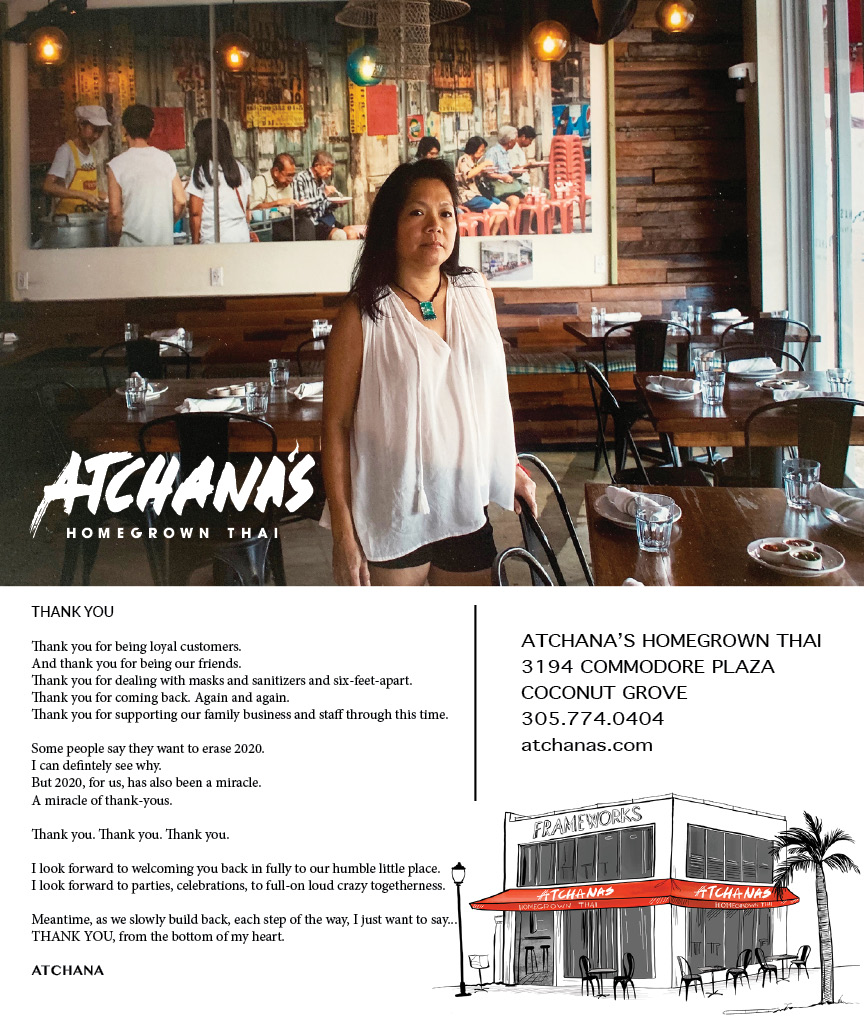
 Baptist Health South Florida
Baptist Health South Florida
 Laser Eye Center of Miami
Laser Eye Center of Miami
 Visiting Angels
Visiting Angels
 OpusCare of South Florida
OpusCare of South Florida


 Your Pet’s Best
Your Pet’s Best
 HD Tree Services
HD Tree Services
 Hamilton Fox & Company
Hamilton Fox & Company

 Creative Design Services
Creative Design Services


